Power generation, transmission and distribution networks are critical to society’s energy supply infrastructure. Accura helps to preserve and protect these vital services to ensure continuity and reliability, and securely capture the benefits of automation and smart technology.
For this sector we have delivered:


The oil and gas sector infrastructure is essential to services and supply chains that we all depend on. Oil and gas companies run complex onshore and offshore operations, where safety is of paramount importance to people and the environment. Environments are becoming more and more complex and digitalized, although it's also a sector which is accompanied by a variety of security challenges.
For this sector we have delivered:
The chemical sector is one of the most important and diverse industries in the world. It includes the production and processing of chemicals and materials that are the basis for a wide range of products and applications. Any disruption to production in this sector can have serious consequences, such as disrupting supply chains or even endangering public health and safety. Therefore, it is necessary to protect functional safety in dangerous environments, protection of intellectual property, and protection of reliable production in chemical production facilities.
For this sector we have delivered:

Water & waste management includes infrastructure for the collection, treatment, and distribution of water and is a key part of any country's critical infrastructure. This sector ensures safe access to drinking water for the population, industrial use, as well as the drainage and treatment of waste water. From a cyber security perspective, the water sector is extremely important, as any disruption to its operations can have serious consequences for public health, the environment, and national security.
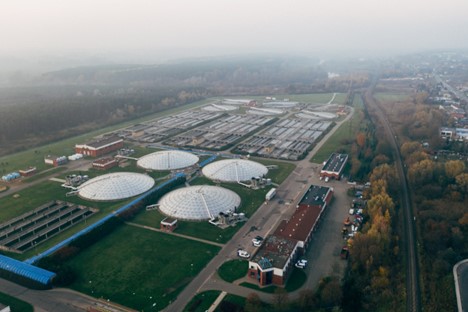
For this sector we have delivered:
Manufacturing spans a wide range of industries, including automotive, electronics, food, engineering, and many others. These businesses play a key role in the global economy by providing goods and products that are essential for daily life, industrial production, and other industries. However, manufacturing is statistically the industry most affected by ransomware attacks. The Internet of Things (IoT) and robotics are improving the efficiency, productivity, and quality of production. These systems are often connected to IT networks, making them vulnerable to cyber attacks.
For this sector we have delivered:
